DEF CON Infosec super-band the Cult of the Dead Cow has released Veilid (pronounced vay-lid), an open source project applications can use to connect up clients and transfer information in a peer-to-peer decentralized manner.
The idea being here that apps – mobile, desktop, web, and headless – can find and talk to each other across the internet privately and securely without having to go through centralized and often corporate-owned systems. Veilid provides code for app developers to drop into their software so that their clients can join and communicate in a peer-to-peer community.
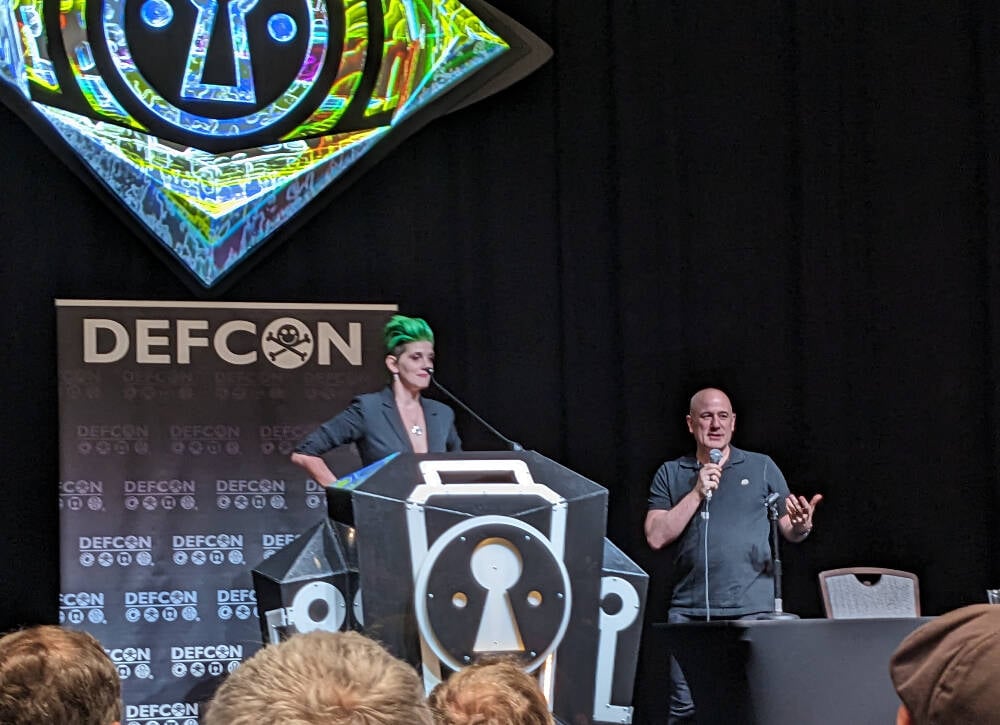
In a DEF CON presentation today, Katelyn “medus4” Bowden and Christien “DilDog” Rioux ran through the technical details of the project, which has apparently taken three years to develop.
The system, written primarily in Rust with some Dart and Python, takes aspects of the Tor anonymizing service and the peer-to-peer InterPlanetary File System (IPFS). If an app on one device connects to an app on another via Veilid, it shouldn’t be possible for either client to know the other’s IP address or location from that connectivity, which is good for privacy, for instance. The app makers can’t get that info, either.
Veilid’s design is documented here, and its source code is here, available under the Mozilla Public License Version 2.0.
“IPFS was not designed with privacy in mind,” Rioux told the DEF CON crowd. “Tor was, but it wasn’t built with performance in mind. And when the NSA runs 100 [Tor] exit nodes, it can fail.”
Unlike Tor, Veilid doesn’t run exit nodes. Each node in the Veilid network is equal, and if the NSA wanted to snoop on Veilid users like it does on Tor users, the Feds would have to monitor the entire network, which hopefully won’t be feasible, even for the No Such Agency. Rioux described it as “like Tor and IPFS had sex and produced this thing.”
“The possibilities here are endless,” added Bowden. “All apps are equal, we’re only as strong as the weakest node and every node is equal. We hope everyone will build on it.”
Each copy of an app using the core Veilid library acts as a network node, it can communicate with other nodes, and uses a 256-bit public key as an ID number. There are no special nodes, and there’s no single point of failure. The project supports Linux, macOS, Windows, Android, iOS, and web apps.
Veilid can talk over UDP and TCP, and connections are authenticated, timestamped, strongly end-to-end encrypted, and digitally signed to prevent eavesdropping, tampering, and impersonation. The cryptography involved has been dubbed VLD0, and uses established algorithms since the project didn’t want to risk introducing weaknesses from “rolling its own,” Rioux said.
This means XChaCha20-Poly1305 for encryption, Elliptic curve25519 for public-private-key authentication and signing, x25519 for DH key exchange, BLAKE3 for cryptographic hashing, and Argon2 for password hash generation. These could be switched out for stronger mechanisms if necessary in future.
Files written to local storage by Veilid are fully encrypted, and encrypted table store APIs are available for developers. Keys for encrypting device data can be password protected.
“The system means there’s no IP address, no tracking, no data collection, and no tracking – that’s the biggest way that people are monetizing your internet use,” Bowden said.
“Billionaires are trying to monetize those connections, and a lot of people are falling for that. We have to make sure this is available,” Bowden continued. The hope is that applications will include Veilid and use it to communicate, so that users can benefit from the network without knowing all the above technical stuff: it should just work for them.
To demonstrate the capabilities of the system, the team built a Veilid-based secure instant-messaging app along the lines of Signal called VeilidChat, using the Flutter framework. Many more apps are needed.
If it takes off in a big way, Veilid could put a big hole in the surveillance capitalism economy. It’s been tried before with mixed or poor results, though the Cult has a reputation for getting stuff done right. ®


You really can’t have it both ways. It’s morally bankrupt to launch protocols that clearly will be used for abhorrent purposes and simply hand wave it away because you’re uncomfortable with the reality of the situation.
I think we all wish that weren’t the case, but it is.
Saying crap like it wouldn’t be a problem if law enforcement would just “git gud” makes you complicit
I agree that you can’t have it both ways; for everyone to have privacy, horrible people have to get privacy, and they will do horrible things with it.
The thing is, people doing horrible things are already incentivized to take precautions, and it’s not possible to uninvent cryptography. Making it more accessible helps the innocent more than it does the guilty.
Source?
Common sense? Take the signal protocol. Theres more innocent people using it for whatever purpose than there are guilty people using it for whatever purpose. You can’t not develop or use a technology just because somebody else might use it for nefarious purposes. Bad people do bad things on the normal internet, does that mean we should start restricting internet usage because someone might do something bad? Of course not, thats just stupid. So why doesn’t the same hold true for encryption technologies? Sure someone with ill intentions is going to do things with it we don’t like, but the majority of users are just wanting to use said technology so governments and corporations don’t see what they are doing.
Or are we not entitled to privacy simply because some people use their privacy to harm others?
There’s literally no way you can back up any of these claims. It’s just what you want to be true.
All I want is for you to admit that you think protecting the “privacy” of people’s mundane text conversations is worth enabling Terrorism, Child Sexual Abuse, Human Trafficking, Organized Crime, etc etc etc
To be clear, I think people should have a basic expectation of privacy. But at what cost? Like we’ve established it’s impossible to have one without the other.
Ok. Cars can be used to ram raid buildings, to try to rip atm from walls. Used to package, carry and execute bombings. Should we ban all vehicles? Or better yet, guns. They can be used, and are used over and over again to attack and terrorise innocent people out at the shops or going to school. Should all guns be banned? The internet can be used to learn how to make bombs and other weapons for the use of terror. That doesn’t even need to be anything special either, simple google searches will get you there. Should we ban the internet. I’m sure there are clearnet sites that post things that shouldn’t be posted its not just on the darknet.
I do agree with your last point though. You can have full security or you can have full privacy but you can’t have both. I think the main argument is because you value security more whilst myself and others value privacy more. Both, in my view are fair and valid.
We have good examples already of people hosting despicable things on TOR hidden services (or the “dark web” if you prefer). On occasion they get caught and we read about it in the news. TOR is old enough to drink in the USA. PGP is decades old and has open source implementations, but takes a bit of effort to use. People who are motivated to secure the content of communications have been able to do so effectively for a long time, and those technologies aren’t about to be uninvented.
Tools like Signal and Veilid make strong privacy protections accessible to the average person. My mother uses Signal. Let’s assume most of us agree that it would be worth giving up those protections to eliminate the use of telecommunication for terrorism, child sexual abuse, human trafficking, and organized crime.
How do you propose to do that when extant open source code has long provided similar capabilities to those motivated enough to put in the effort to use it?
So if a predator locks a victim in a closet, does that make lockmakers morally reprehensible?
Locks don’t make predators untraceable
But they do offer an easy, quick and convienient way for a predator to contain their victim, much simpler than tying them down or holding them.
Gonna have to agree to disagree here: to my mind, taking away tools that allow people to evade the restrictions of unjust regimes because you buy into the “for the children” fear mongering makes you complicit in the rising totalitarian state.
Just because people use “for the children” in inappropriate scenarios to further an agenda has nothing to do with this discussion and you know it.
If you make a tool to essentially hide people’s activity online, you KNOW what it’s going to ultimately be used for.
…and you clearly think it’s worth the trade off. So no need to continue